ITAR compliance checklist: Everything you need to know [Guide]

You may have already heard about GDPR and CCPA compliance and what it involves when it comes to consumer data in our rapidly changing digital world. But how much do you know about the International Traffic in Arms Regulations (ITAR)?
ITAR Compliance
The ITAR was passed into law by the US government to limit access to physical materials or technical data related to defense and military technologies. Considering how easily sensitive information can end up in the wrong hands, this was a necessary step for everyone’s safety.
In this article, we’ll break down what this regulatory compliance implies and which businesses need to comply with it. We’ve also put together a quick ITAR compliance checklist.
- What is ITAR (International Traffic in Arms Regulations)?
- Who needs to be ITAR-compliant?
- How can you be ITAR-compliant?
- What is an ITAR visitor logbook?
- What are the ITAR penalties?
- Summary: ITAR compliance checklist
1. What are ITAR regulations?
The International Traffic in Arms Regulations (ITAR) is the US regulation that controls the manufacture, sale, and distribution of defense articles, services, and technology as defined in the United States Munitions List (USML).
Generally, ITAR is enforced by the Directorate of the Defense Trade Controls (DDTC) in the State Department.
There are 21 categories of defense articles mentioned in the USML as follows:
- Firearms, close assault weapons, and combat shotguns
- Guns and armament
- Ammunition/ordnance
- Launch vehicles, guided missiles, ballistic missiles, rockets, torpedoes, bombs, and mines
- Explosives and energetic materials, propellants, incendiary agents, and their constituents
- Surface vessels of war and special naval equipment
- Ground vehicles
- Aircraft and related articles
- Military training equipment and training
- Personal protective equipment
- Military electronics
- Fire control, laser, imaging, and guidance equipment
- Materials and miscellaneous articles
- Toxicological agents, including chemical agents, biological agents, and associated equipment
- Spacecraft and related articles
- Nuclear weapons-related articles
- Classified articles, technical data, and defense services not otherwise enumerated
- Directed energy weapons
- Gas turbine engines and associated equipment
- Submersible vessels and related articles
- Articles, technical data, and defense services not otherwise enumerated
While defense services involve the following:
- providing assistance, including training, to foreign persons on anything related to the design, development, engineering, manufacture, production, assembly, testing, repair, maintenance, modification, operation, demilitarization, destruction, processing, or use of defense articles
- providing foreign persons with controlled technical data
- military training of foreign units and forces.
Technical data includes elements such as:
- information other than software for the design, development, production, manufacture, assembly, operation, repair, testing, maintenance or modification of defense articles (this information can be in the form of blueprints, photographs, plans, and more).
- classified information about the defense articles and defense services listed above
- software directly related to defense articles
2. ITAR compliance and requirements
These parties must be fully aware of and fully compliant with ITAR.
- Any company that does business with the U.S. military
- Any organization that deals with information concerning defense articles, services, or related data mentioned in the USML
And what of third-party contractors?
Third-party contractors are also subjected to ITAR regulations that work with them and all the other companies in the supply chain, including:
- Wholesalers
- Distributors
- Tech companies
- Third-party suppliers
- Contractors
 The basic rule that all the parties mentioned above have to follow is this: only U.S. citizens can access items on the USML list.
The basic rule that all the parties mentioned above have to follow is this: only U.S. citizens can access items on the USML list.
“U.S. person means a person who is a lawful permanent resident or who is a protected individual. It also means any corporation, business association, partnership, society, trust, or any other entity, organization or group that is incorporated to do business in the United States. It also includes any governmental (federal, state or local) entity.” - ITAR, Section 120.15
Note: There are certain countries that currently have standing agreements with the U.S. that apply to ITAR, such as Australia, Canada, and the U.K.
Let’s move on to the next step and delve into what you should keep in mind when getting yourself ITAR-ready.
3. How to comply with ITAR requirements
Once you've determined that ITAR applies to your business, the first step toward becoming compliant is to register with the DDTC.
There is a non-refundable fee associated with registration and also a few important points to remember:
- You are required to renew your ITAR registration every 12 months.
- You should submit your ITAR registration renewal documents at least 60 days prior to the expiration date of your registration.
This way, you’ll have your documents processed and approved before the deadline.
Key tip: To keep your ITAR registration up to date, you should designate a person in your company responsible for managing the renewal each year.
Post-registration: next steps
It’s time to create and implement a documented ITAR compliance program, which should include tracking, monitoring, and auditing of technical data. When it comes to technical data, it’s essential to train your employees in understanding what type of controlled information has to be kept safe from unauthorized users.
The DDTC defines a good program as being “clearly documented in writing, tailored to the business, regularly reviewed/updated and fully supported by management”.
In short: As secure as possible. Also, companies that manage ITAR regulated materials and data can follow the guidelines for data security provided in the NIST SP 800-53.
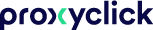
There are a few basic principles you can follow to secure your ITAR-related data:
- Discover and classify sensitive data - make sure to locate and secure all sensitive data and classify it based on your business policy
- Map data and permissions - take time to identify all the users, groups, folder, and file permissions involved in your data handling process and clearly determine who has access to what data
- Manage access control on your data - identify and deactivate stale users and manage user and group memberships to improve the security of your file-sharing process
- Monitor data, file activity, and user behavior to prevent any threats, malware, misconfigurations, and security breaches that might appear
Note: The new ITAR encryption rule that came into effect on March 25, 2020 releases the transmission of unclassified defense technical data using end-to-end encryption from ITAR control.
However, the foreign person who receives the technical data has to be authorized before they are provided with the access information that allows them to access that data in unencrypted form.
4. What does ITAR mean for visitor management?
A key element in showing ITAR compliance is visitor scanning, tracking and record-keeping—core functions of a visitor management system. We could even call it an ITAR visitor logbook.
So what is an ITAR visitor logbook?
Is there such a thing as an ITAR-compliant visitor logbook? Sure there is.
A cloud-based visitor management system like Proxyclick can provide your business with the vital elements required and create a seamless and secure check-in experience for your visitors.
In addition to regulatory compliance with many other global laws, Proxyclick can help you manage your visitors around the following ITAR compliance requirements:
- Make pre-registration of all visitors and contractors mandatory
- Use facial recognition technology for identity verification at check-in with our
ID Match feature - Verify countries of origin or citizenship of your visitors
- Customize check-in flows based on the purpose of the visit and the level of authorization needed
- Screen visitors against watchlists to ensure authorization
- Alert security if unauthorized access is attempted
- Capture digital signatures on legal documents and NDAs
- Customize and print visitor badges with photos, QR codes for access, etc.
- Implement access control to areas of your premises with access control integrations
- Track visitor history and their precise movements for reporting and audit purposes
- Export data for all insurance- and audit-related queries
5. What are the penalties for ITAR compliance violations?
Non-compliance with the ITAR regulation can result in significant fines, brand and reputation damage, and even potential loss of business to a competitor who's on top of their corporate governance.
The penalties for ITAR violations include civil fines up to $500,000 per violation and criminal fines of up to $1 million and/or 10 years imprisonment per violation.
6. ITAR compliance checklist
Bearing in mind that no two companies are exactly alike, here's a good starting point to use as your ITAR checklist:
- Determine whether or not the International Traffic in Arms Regulations government agency has jurisdiction over your products.
- Review ITAR and its requirements in full (e.g., classification, record-keeping requirements, and export license requirements).
- Register your company with the DDTC.
- Classify and designate your products according to the U.S. Munitions List.
- Screen all parties and stay on top of who your end users are.
- Set up a cloud-based visitor management system to help you.
- Apply for an Export License and ensure you comply with all export procedures.
- Fulfill all reporting requirements (e.g., sales fees, commissions relating to all ITAR-control items).
- Create and maintain an Export Management and Compliance Program.
Note: Considering all regulations can change over time, you should regularly revisit and revise your ITAR compliance measures.
Look out for April
An annual edition of ITAR regulations is published each April, however, you shouldn’t wait until then to familiarize yourself with the ITAR compliance requirements.
Changes within your company—a new partnership with another organization or the introduction of a new data-sharing application—are a great opportunity to revisit ITAR regulations and make sure that all your processes and business partners are 100% compliant.
Becoming compliant and maintaining that status on a day-to-day basis can require significant efforts, but consider us a trusted partner in helping you meet your compliance objectives.
Useful resources
Find out more about how a visitor management system can help you on your compliance journey:
- How QR code sign-in systems can support your business right now
- Why you should integrate your access control system with Proxyclick
- How to implement a touchless check-in experience
To learn more about how Proxyclick helps future-proof the workplace, book a call with one of our experts.
***
Disclaimer: The information presented above is not legal advice, is not to be acted on as such, may not be current and is subject to change without notice. You should seek professional legal counsel before taking any action.